
How VPN Fleet Protects Your Privacy: A Technical Deep Dive
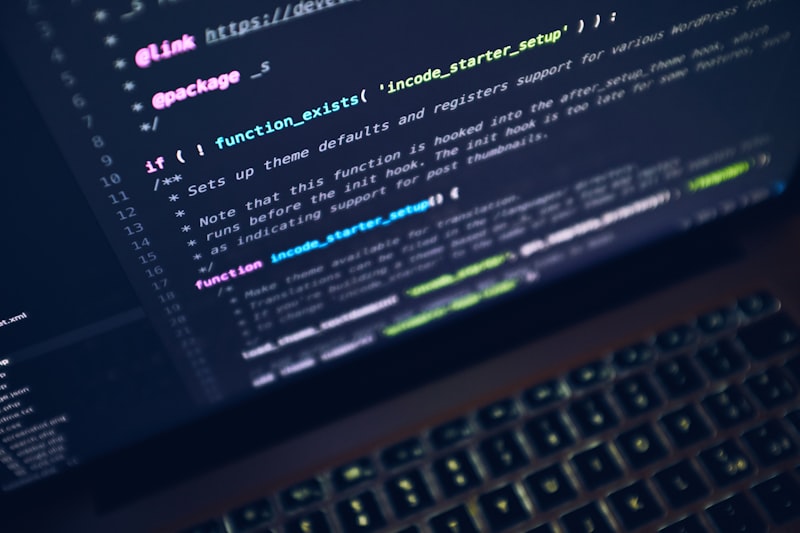
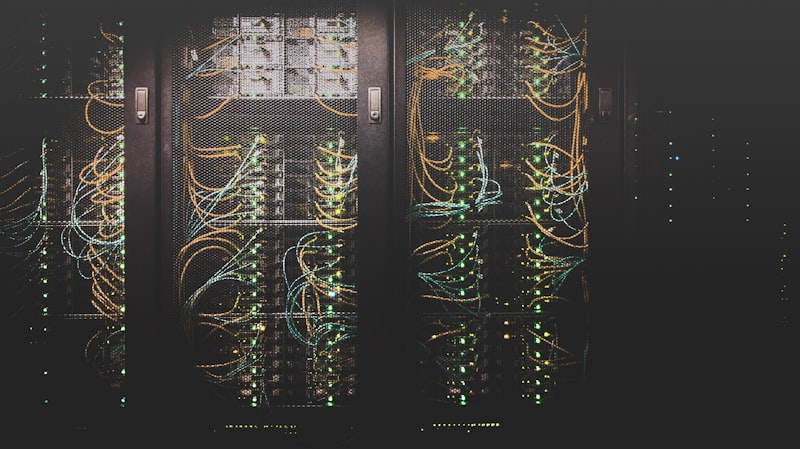
A behind-the-scenes look at our RAM-only servers, encryption stack, and no-log architecture.
Insights, tutorials, and updates from our team.

A behind-the-scenes look at our RAM-only servers, encryption stack, and no-log architecture.
Working from Bali, Lisbon, or Bangkok? Here's how to stay secure and access your tools from anywhere in the world.

Split tunneling lets you route some traffic through VPN while keeping other traffic direct. Learn when this powerful feature makes sense.

A comprehensive security checklist for distributed teams. From VPN setup to access control best practices.
From AI-powered phishing to quantum computing threats, here are the biggest cyber risks you need to know about.

How to use a VPN to access geo-restricted streaming content while traveling. Tips for optimal streaming performance.

What makes AES-256 the encryption standard trusted by governments and military organizations worldwide? A technical explainer.

Public Wi-Fi networks are a goldmine for hackers. Learn how to protect yourself with these essential security practices.
A deep dive into the two most popular VPN protocols. Performance benchmarks, security analysis, and when to use each.